Business network security is now a central operational priority for organizations that depend on digital systems to operate and grow.
As you expand into cloud platforms, SaaS applications, and hybrid work environments, the traditional boundaries of your network begin to disappear.
What once relied on perimeter firewalls and internal trust models now requires a more structured and proactive approach to cybersecurity for business.
At the same time, the threat landscape continues to evolve.
Ransomware groups increasingly target business infrastructure, while attackers use automated tools and AI-assisted techniques to scan for vulnerabilities and launch attacks at scale.
Even if you’re well resourced, you can face significant exposure if network architecture, monitoring, and governance don’t evolve alongside the technology environment.
So, this article will show how business network security has to be a core part of operational resilience and risk management for long-term business continuity.
Table of contents
Why Business Network Security is More Critical Than Ever
Core Components of Business Network Security
Business Network Security Best Practices
Common Business Network Security Mistakes
Why Network Security Requires a Strategic Approach
Network Security Solutions: In-House vs. Managed Services
Why Business Network Security Is More Critical Than Ever
The role of business network security has changed significantly. Cloud platforms, remote access, and interconnected systems mean your network is more complex and far more exposed than ever.
Hybrid work is one of the biggest drivers of this shift.
Employees now access company systems from homes, mobile devices, and public networks – which expands the number of entry points attackers may attempt to exploit.
At the same time, businesses increasingly rely on SaaS platforms, cloud infrastructure, and third-party integrations that extend the network beyond a single physical location.
Threat actors have also become more sophisticated. Many are harvesting data now in order to decrypt it later, when quantum computers can break the current security systems.
Ransomware groups now specifically target operational systems and enterprise infrastructure, knowing that downtime can quickly disrupt revenue and business continuity.
In many cases, attackers use automated tools and AI-assisted scanning to identify exposed systems and vulnerabilities at scale.
Agentic AI in your workflows will increase risk if not governed tightly.
Regulatory expectations are also increasing. Cybersecurity for business now affects compliance requirements, cyber-insurance coverage, and contractual obligations with partners and clients.
As a result, business network security plays a central role in your overall business cybersecurity strategy and long-term operational resilience.
Core Components of Business Network Security
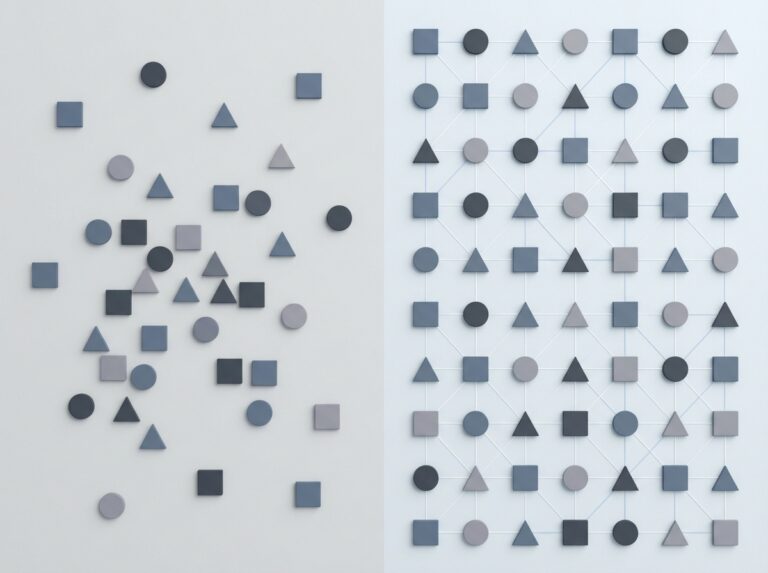
You can’t build effective business network security around a single product or tool. You should depend on a layered architecture that protects your systems, data, and users at multiple points across your environment.
As your infrastructure expands across offices, cloud platforms, and remote access points, security controls must work together to provide consistent visibility and protection.
If you treat security as having a single perimeter, attackers can move freely once they gain access.
The strongest approach therefore combines multiple layers of defense so that vulnerabilities in one area don’t expose the entire network.
This layered model is now widely used in enterprise network security environments and is increasingly essential for mid-market growing companies as well.
Firewall Architecture and Network Segmentation
Older firewall architecture filtered basic traffic. Next-generation firewalls inspect application behavior, monitor encrypted traffic, and enforce granular policies across users and systems.
Network segmentation is equally important. By separating your systems into controlled network zones – often using virtual local area networks (VLANs) or similar approaches – you reduce the risk of lateral movement if an attacker gains access to one device or service.
These firewall security best practices help contain potential breaches and protect critical systems from unnecessary exposure.
Zero Trust Network Security
Traditional networks assumed that once a user or device entered the internal network, it could be trusted. Today, that’s not safe.
Zero Trust security models require every user, device, and application to verify identity and authorization before accessing resources.
Access is granted based on least-privilege principles and contextual signals such as device health, location, and authentication strength.
Increasingly, Zero Trust is becoming the baseline architecture for enterprise network security management – particularly as remote access and cloud services expand.
Endpoint Detection and Response
Perimeter defenses alone can’t stop every threat. Attackers frequently gain entry through compromised credentials, phishing campaigns, or vulnerable devices.
Endpoint Detection and Response (EDR) tools monitor devices continuously for suspicious behavior, allowing security teams to detect and contain threats before they spread.
This visibility is critical because endpoints – laptops, servers, and mobile devices – often represent the most common entry points into a network.
Continuous Network Monitoring
Strong business network security also depends on continuous overall monitoring to detect unusual behavior, unauthorized access attempts, or emerging threats.
Modern, effective network security monitoring relies on centralized logging, security information and event management (SIEM) platforms, and security operations centers that analyze all activity across your environment.
This continuous monitoring allows you to identify risks earlier and respond before small issues escalate into significant incidents.
Together, these components form the layered architecture behind effective solutions for cybersecurity.
Business Network Security Best Practices
Effective business network security depends on consistent operational discipline. Even the most advanced tools can’t protect your organization if basic security practices are inconsistent or poorly enforced.
For growing companies, the challenge is often scale.
Your networks expand, your systems multiply, remote access increases, and new applications come into use.
Without clear governance and structured network security management, gaps can appear quickly.
The following network security best practices form the operational foundation of a resilient security environment and help you understand how to secure a business network as it grows.
- Segment networks to limit lateral movement between systems and environments.
- Maintain consistent patch and vulnerability management across infrastructure.
- Enforce multi-factor authentication for remote access, administrative accounts, and critical systems.
- Implement strict identity and access control policies based on least-privilege principles.
- Harden VPN and remote access configurations to reduce exposure.
- Maintain secure, tested backup and recovery processes to support rapid restoration after incidents.
- Deploy continuous network security monitoring to identify suspicious activity quickly.
- Conduct regular security audits and vulnerability assessments.
- Maintain documented incident response and recovery procedures.
When these practices operate together, they create the layered protection that effective network security requires.
Rather than relying on a single defensive control, multiple safeguards work together to reduce risk and improve your ability to detect and contain threats early.
Common Business Network Security Mistakes
Even when you invest in modern tools, gaps in network security can still appear.
Often this will be because you haven’t coordinated your systems, policies, and oversight within a clear strategy – a cohesive architecture.
One common mistake is maintaining a flat network structure.
Lack of segmentation means access to a single device opens up your entire environment. Clearly defined network zones help you limit the impact of a breach and protect critical systems.
You may also rely too heavily on a single defensive layer, such as antivirus software or a basic firewall.
But modern threats rarely depend on one technique. Attackers frequently combine phishing, credential theft, and vulnerability exploitation to bypass traditional defenses.
Effective cybersecurity solutions for businesses rely on layered controls that work together across the network.
Tool sprawl can create another problem.
As you add new security products over time, it becomes harder to maintain consistent policies and visibility. Without strong network security management, disconnected tools can generate alert fatigue in your staff – while still leaving gaps in protection.
New risks are also emerging as employees experiment with unsanctioned (shadow) AI tools or automated workflows that connect directly to company data.
If these systems operate outside normal security oversight, they can introduce unexpected access paths.
Ultimately, effective business network security depends on proactive monitoring and structured oversight.
When you rely only on reactive support – fixing problems after they occur – you leave your organization exposed to threats that could have been detected much earlier.
Avoiding these mistakes requires a clear and coordinated security strategy.
Why Network Security Requires a Strategic Approach
As your organization grows, business network security becomes less about individual tools and more about how those tools, policies, and processes work together within a defined strategy.
Firewalls, monitoring platforms, and endpoint protection all play important roles. But without coordination, they rarely provide the level of protection you expect.
Effective cyber security for business therefore depends on a structured strategy.
Security controls must align with how your organization operates – how employees access systems, how data moves across networks, and how cloud services integrate with internal infrastructure.
This broader view connects business and cybersecurity decisions directly to operational risk and continuity planning.
You also need visibility across the entire environment. Continuous monitoring, consistent policies, and clear accountability allow you to detect suspicious activity early and respond before an issue escalates.
For many growing companies, this level of coordination requires more than internal tools alone. You need an approach to network security management that combines technical expertise, ongoing monitoring, and strategic oversight.
One possibility is to consider managed IT services instead of, or as well as, in-house teams.
Network Security Solutions: In-House vs. Managed Services
As your systems grow more complex, maintaining strong business network security internally can become difficult to sustain.
You may already rely on internal IT staff to manage infrastructure, support users, and maintain systems.
Adding continuous security monitoring, threat detection, and incident response can quickly stretch those resources.
Building a full internal security capability also requires specialist expertise and round-the-clock monitoring.
That combination can be difficult to maintain consistently. Which explains why cyber risk and cybersecurity risk assessment is now a board-level business issue, not just an IT concern.
This is why you may want to evaluate a mix of internal oversight and external expertise.
Modern network security solutions often involve partnering internal IT leadership with managed network security services that provide 24/7 monitoring, threat detection, and operational support.
Predictability of cost is an important decision point here when considering managed IT services vs. internal IT support.
Katalyst Can Supply Managed Business Network Security Solutions
Katalyst partners with you as a strategic advisor to assess your environment, improve visibility across your systems, and implement practical cybersecurity solutions for businesses that we tailor to your operational goals.
Why Katalyst? We’re engineering-led and security-first. We’re also vendor-agnostic – outcome driven rather than linked to specific tools.
If you want a security strategy that supports you as you grow, schedule a network security assessment with us today.