If you’re looking for cybersecurity solutions Charlotte mid-sized businesses can actually rely on, preventing hackers is only one part of the picture. You also need to protect uptime, data, client trust, and the systems your business depends on every day.
This kind of cybersecurity is now an operational issue as much as a technical one for the many growing companies in Charlotte, NC.
Financial firms, healthcare organizations, manufacturers, and other mid-sized businesses are managing more cloud systems, more endpoints, more vendors, and more exposure than ever before.
At the same time, attackers are getting faster, more automated, and more opportunistic.
That means a basic firewall and antivirus package are no longer enough.
Today, effective cybersecurity for Charlotte businesses must cover prevention, detection, response, recovery, and the policies behind them.
It also has to fit the realities of a mid-market organization: lean internal teams, compliance pressure, and no prolonged downtime.
In this guide, we’ll break down the threats facing businesses across North Carolina, what modern cybersecurity protection actually includes, and how you can protect your operations.
Table of contents
Why Cybersecurity Solutions Are Critical for Charlotte Businesses
The Most Common Cybersecurity Threats Facing Charlotte Companies
What Cybersecurity Solutions for Businesses Actually Include to Protect Your Operations
In-House vs. Managed Cybersecurity Services in Charlotte
How to Choose the Right Cybersecurity Provider in Charlotte, NC
Why Cybersecurity Solutions Are Critical for Charlotte Businesses
The growth of Charlotte as a major business and financial center in North Carolina has brought additional digital risk with it.
As you add cloud platforms, remote access, connected devices, third-party vendors, and larger volumes of sensitive data, the number of ways an attacker can get in also increases.
It’s easy to underestimate those risks. You may not have a full security function with the time, tooling, and 24/7 visibility to keep up with today’s threat landscape.
That leaves gaps in monitoring, access control, endpoint protection, user behavior, and incident response.
Growing businesses in Charlotte and across North Carolina are also under pressure to prove they can protect data and maintain continuity.
Sectors such as financial services, healthcare, manufacturing, and other regulated or operationally complex environments need stronger security – not only to prevent a breach, but to keep the business running when systems, people, and vendors are all connected.
The cost of getting it wrong is business-wide.
Downtime, ransomware, account compromise, and data loss can interrupt your operations, affect customer trust, trigger compliance issues, and create expensive recovery work after the event.
That’s why cybersecurity solutions in Charlotte need to:
- Help reduce risk
- Strengthen resilience
- Protect day-to-day operations before disruption spreads
The Most Common Cybersecurity Threats Facing Charlotte Companies
In many cases, cyber threats begin with a routine email, a reused password, an overlooked system update – or one of your users clicking something at the wrong moment.
But once inside your environment, the impact can spread quickly across your operations, data, and customer service.
For Charlotte businesses, the most serious risks are usually the ones that interrupt how work gets done:
Ransomware Attacks
Ransomware remains one of the most disruptive threats for mid-sized organizations. Attackers today often steal data, move across the network, and target backups or critical systems before making demands.
For a financial firm, that could mean loss of access to internal records or client systems.
In a healthcare organization, it could delay scheduling, access to records, or care coordination.
For a manufacturer, it can affect production, shipping, inventory, or supplier communication.
Ransomware protection now depends on layered controls, fast threat detection and response, strong access management, and recovery planning that you’ve actually tested.
Phishing and Social Engineering
Many security incidents still start with people being “tricked” rather than your systems being hacked. That means: phishing emails, fake login pages, impersonation attempts, and business email compromise attacks. These can look normal enough to get past a busy employee.
Attacks are especially effective when staff are moving quickly, handling invoices, sharing documents, approving payments, or managing customer information across multiple platforms.
For Charlotte companies with hybrid teams or growing vendor networks, phishing is an operational risk. It can lead to credential theft, wire fraud, account compromise, and wider network access.
Insider Threats and Human Error
Sometimes the risk comes from inside your organization – through negligence, poor access controls, accidental data exposure, or former employees retaining access longer than they should.
This is common where systems expand faster than internal processes can keep up. Shared logins, broad permissions, shadow IT, and inconsistent offboarding all create unnecessary exposure.
For regulated industries in North Carolina, this is especially important. A preventable internal mistake can still become a costly compliance issue, a legal issue, or a client trust issue.
Network Vulnerabilities
Your own infrastructure can also carry hidden risks.
Older firewalls, poorly segmented networks, unpatched systems, exposed remote access tools, and unmanaged devices can all create entry points for attackers.
This matters even more in environments where uptime is critical. In manufacturing, logistics, healthcare, and multi-site operations, one weak point in the network can affect far more than a single user or device.
For Charlotte businesses, that means you need proactive security. If vulnerabilities are only discovered after a disruption, the damage is usually already underway.
What Cybersecurity Solutions for Businesses Actually Include to Protect Your Operations
If you’re evaluating cybersecurity solutions for Charlotte businesses, it helps to look beyond individual tools.
Real protection comes from how those controls work together across your users, devices, network, data, and day-to-day operations.
A strong security program should include the following as a minimum:
Network Security and Firewall Protection
Your business network is still one of the first places to establish control. That includes firewalls, secure remote access, network segmentation, and policies that limit how easily an attacker can move from one system to another.
This is where hidden risk builds up over time.
Offices expand, you add cloud services, you connect more vendors, and remote users need access. But your security architecture doesn’t always evolve at the same pace.
Strong network security helps design your environment to contain threats before they spread.
Endpoint Detection Response (EDR) and Managed Detection Response (MDR)
Laptops, desktops, servers, and mobile devices are all potential entry points.
Endpoint security today should include the ability to detect unusual activity, investigate it quickly, and respond before a device becomes the starting point for a wider incident.
EDR and MDR services help identify threats earlier and give you a better chance of stopping an issue before it affects operations.
24/7 Monitoring and Threat Detection
Most cyber incidents don’t happen conveniently. Attackers often look for quiet windows, overnight access, or gaps in visibility where suspicious activity can go unnoticed.
24/7 monitoring gives you visibility into what’s happening across your environment – along with a documented process for investigating alerts and acting on them.
For mid-sized businesses, this is often one of the biggest gaps between having some security tools and having a real security capability.
Data Backup and Disaster Recovery
Good cybersecurity is also about resilience. If a ransomware event, outage, or destructive error does happen, you need to know how quickly your systems and data can be recovered.
That means backups should be secure, monitored, tested, and separated from the systems they’re designed to protect.
Disaster recovery planning should also be tied to business priorities, so your most critical operations can be restored first.
Recovery speed is not only a technical metric but something that affects your service delivery, revenue, and customer confidence.
Identity and Access Management
Many security incidents begin with legitimate credentials being used in the wrong way.
That could mean a stolen password, a compromised admin account, weak multi-factor authentication, or access rights that were never tightened as your business grew.
Identity and access management helps control who can access what, when, and under what conditions.
That includes stronger authentication, role-based access, conditional access policies, and zero trust security principles that reduce unnecessary exposure.
If you’re managing growth, multiple systems, and distributed teams, this is one of the most practical ways to reduce risk without disrupting productivity.
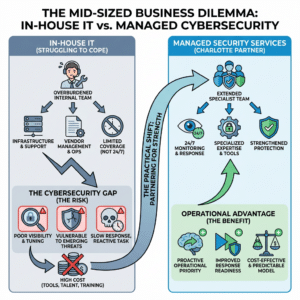
In-House vs. Managed Cybersecurity Services in Charlotte
Many mid-sized businesses already have internal IT support, but cybersecurity creates a different level of demand and skills.
Protecting users, endpoints, networks, identities, and data requires ongoing attention, specialist knowledge, and the ability to respond quickly when something unusual appears.
That’s often difficult for internal teams to carry alone, especially when they’re also responsible for infrastructure, support, vendor management, and day-to-day operations.
There’s the issue of coverage as well.
Most internal teams are not built for 24/7 monitoring, investigation, and response. Even strong IT departments can struggle to maintain visibility, tune security tools properly, stay current on emerging threats, and close gaps before they become incidents.
Cost is another factor.
Building a mature in-house security capability often means investing in multiple tools, specialist talent, training, processes, and after-hours coverage.
For many organizations, that’s difficult to justify unless security is already a dedicated function.
This is where a more practical model is to partner with managed security services Charlotte businesses can benefit from.
The right partner can extend your internal team, strengthen protection, improve response readiness, and help you approach cybersecurity as an operational priority rather than a reactive IT task.
How to Choose the Right Cybersecurity Provider in Charlotte, NC
When you’re comparing cybersecurity solutions in Charlotte, NC, the key question is how well a provider can help you reduce risk, support operations, and make better long-term security decisions.
Look for experience in regulated or operationally complex environments. Financial firms, healthcare organizations, manufacturers, and multi-site businesses all face different pressures, and those realities should shape the security approach.
It’s also worth looking at how the provider works. A security-first, engineering-led approach is very different from a reactive model that only responds once something breaks.
The right cybersecurity company in Charlotte should be able to strengthen your environment proactively, explain risk clearly, and help you prioritize what matters most.
Local understanding matters too. A provider that understands how Charlotte businesses operate – and how growth, compliance, and uptime pressures show up in practice – is better placed to offer practical guidance, not just technical fixes.
Most importantly, choose a partner that can support your business as it evolves.
If you’re looking for cybersecurity consulting in Charlotte, you should expect strategic guidance that helps you plan ahead, improve resilience, and align security decisions with how your business actually runs.
Katalyst Has Cybersecurity Solutions in Charlotte, NC to Protect Your Operations
With today’s broader cybersecurity risks, your operational stakes are higher and the cost of reacting late continues to grow.
If you want a clearer view of your security posture, a cybersecurity risk assessment is a practical place to start. It can help identify gaps, reduce avoidable exposure, and guide your next decisions.
If your business needs proactive cybersecurity solutions in Charlotte, NC, you can speak directly with one of Katalyst’s Charlotte-based experts and take the next step toward strengthening your security. Give us a call today.